 https://compsysplus.com/wp-content/uploads/2024/02/DALL·E-2024-01-21-18.21.59-A-photo-realistic-image-representing-proactive-network-monitoring-as-a-watchful-eye-overseeing-a-network-infrastructure-symbolizing-proactive-prevent.png
1024
1792
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-02-29 06:00:002024-02-08 15:11:41Proactive Network Monitoring: Predicting and Preventing Network Issues
https://compsysplus.com/wp-content/uploads/2024/02/DALL·E-2024-01-21-18.21.59-A-photo-realistic-image-representing-proactive-network-monitoring-as-a-watchful-eye-overseeing-a-network-infrastructure-symbolizing-proactive-prevent.png
1024
1792
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-02-29 06:00:002024-02-08 15:11:41Proactive Network Monitoring: Predicting and Preventing Network IssuesBlog/Insights:
 https://compsysplus.com/wp-content/uploads/2024/02/DALL·E-2024-01-21-18.21.59-A-photo-realistic-image-representing-proactive-network-monitoring-as-a-watchful-eye-overseeing-a-network-infrastructure-symbolizing-proactive-prevent.png
1024
1792
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-02-29 06:00:002024-02-08 15:11:41Proactive Network Monitoring: Predicting and Preventing Network Issues
https://compsysplus.com/wp-content/uploads/2024/02/DALL·E-2024-01-21-18.21.59-A-photo-realistic-image-representing-proactive-network-monitoring-as-a-watchful-eye-overseeing-a-network-infrastructure-symbolizing-proactive-prevent.png
1024
1792
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-02-29 06:00:002024-02-08 15:11:41Proactive Network Monitoring: Predicting and Preventing Network Issues https://compsysplus.com/wp-content/uploads/2024/02/DALL·E-2024-01-21-18.18.34-A-photo-realistic-image-representing-network-management-as-a-blueprint-or-architectural-diagram-emphasizing-planning-and-governance.-The-visual-shoul.png
1024
1792
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-02-22 06:00:002024-02-08 15:09:12Network Monitoring vs. Network Management: Navigating the Distinctions
https://compsysplus.com/wp-content/uploads/2024/02/DALL·E-2024-01-21-18.18.34-A-photo-realistic-image-representing-network-management-as-a-blueprint-or-architectural-diagram-emphasizing-planning-and-governance.-The-visual-shoul.png
1024
1792
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-02-22 06:00:002024-02-08 15:09:12Network Monitoring vs. Network Management: Navigating the Distinctions https://compsysplus.com/wp-content/uploads/2024/02/DALL·E-2024-01-21-18.15.36-A-photo-realistic-image-representing-data-encryption-showcasing-data-being-transformed-into-unreadable-text-as-it-flows-through-a-secure-tunnel.-The-.png
1024
1792
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-02-15 06:00:002024-02-08 15:06:42Ensuring Data Security in Infrastructure Management
https://compsysplus.com/wp-content/uploads/2024/02/DALL·E-2024-01-21-18.15.36-A-photo-realistic-image-representing-data-encryption-showcasing-data-being-transformed-into-unreadable-text-as-it-flows-through-a-secure-tunnel.-The-.png
1024
1792
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-02-15 06:00:002024-02-08 15:06:42Ensuring Data Security in Infrastructure Management https://compsysplus.com/wp-content/uploads/2024/02/DALL·E-2024-01-21-18.08.51-A-photo-realistic-image-representing-a-hacker-attempting-to-breach-a-network-met-with-multiple-layers-of-security-defenses.-The-visual-should-depict-.png
1024
1792
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-02-14 06:00:002024-02-08 15:14:12Securing Your Network: Best Practices in Network Monitoring and Management
https://compsysplus.com/wp-content/uploads/2024/02/DALL·E-2024-01-21-18.08.51-A-photo-realistic-image-representing-a-hacker-attempting-to-breach-a-network-met-with-multiple-layers-of-security-defenses.-The-visual-should-depict-.png
1024
1792
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-02-14 06:00:002024-02-08 15:14:12Securing Your Network: Best Practices in Network Monitoring and Management https://compsysplus.com/wp-content/uploads/2024/02/Screenshot-2024-02-08-at-10.57.17-PM.png
1304
2268
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-02-08 06:00:002024-02-08 15:03:25The Role of Automation in Infrastructure Management
https://compsysplus.com/wp-content/uploads/2024/02/Screenshot-2024-02-08-at-10.57.17-PM.png
1304
2268
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-02-08 06:00:002024-02-08 15:03:25The Role of Automation in Infrastructure Management https://compsysplus.com/wp-content/uploads/2024/01/1-4.png
954
1430
tridigitalSEO
/wp-content/uploads/2023/10/logo.svg
tridigitalSEO2024-02-01 17:59:002024-01-18 12:06:03All You Need to Know about Computer Systems Plus’ Managed IT Services and How They Can Help Your Business
https://compsysplus.com/wp-content/uploads/2024/01/1-4.png
954
1430
tridigitalSEO
/wp-content/uploads/2023/10/logo.svg
tridigitalSEO2024-02-01 17:59:002024-01-18 12:06:03All You Need to Know about Computer Systems Plus’ Managed IT Services and How They Can Help Your Business https://compsysplus.com/wp-content/uploads/2024/02/DALL·E-2024-01-21-18.11.10-A-photo-realistic-image-depicting-cloud-infrastructure-with-data-flowing-seamlessly-between-servers-in-a-virtual-environment.-The-visual-should-show-a.png
1024
1792
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-02-01 06:00:002024-02-08 14:56:01Demystifying Infrastructure Management: A Comprehensive Guide
https://compsysplus.com/wp-content/uploads/2024/02/DALL·E-2024-01-21-18.11.10-A-photo-realistic-image-depicting-cloud-infrastructure-with-data-flowing-seamlessly-between-servers-in-a-virtual-environment.-The-visual-should-show-a.png
1024
1792
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-02-01 06:00:002024-02-08 14:56:01Demystifying Infrastructure Management: A Comprehensive Guide https://compsysplus.com/wp-content/uploads/2024/01/1-3.png
664
1000
tridigitalSEO
/wp-content/uploads/2023/10/logo.svg
tridigitalSEO2024-01-30 16:54:002024-01-18 11:57:36Strategic IT Outsourcing: How Managed Services Boost Business Efficiency
https://compsysplus.com/wp-content/uploads/2024/01/1-3.png
664
1000
tridigitalSEO
/wp-content/uploads/2023/10/logo.svg
tridigitalSEO2024-01-30 16:54:002024-01-18 11:57:36Strategic IT Outsourcing: How Managed Services Boost Business Efficiency https://compsysplus.com/wp-content/uploads/2024/01/Conceptual-image-showing-a-modern-corporate-building.jpg
400
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-01-26 06:00:002024-01-16 15:32:12Enhancing Your Cybersecurity with Computer Systems Plus: The MSP Advantage
https://compsysplus.com/wp-content/uploads/2024/01/Conceptual-image-showing-a-modern-corporate-building.jpg
400
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-01-26 06:00:002024-01-16 15:32:12Enhancing Your Cybersecurity with Computer Systems Plus: The MSP Advantage https://compsysplus.com/wp-content/uploads/2024/01/1-2.png
800
1280
tridigitalSEO
/wp-content/uploads/2023/10/logo.svg
tridigitalSEO2024-01-25 17:51:002024-01-18 11:54:25Cybersecurity in the Age of AI: Transforming IT Solutions for Modern Businesses
https://compsysplus.com/wp-content/uploads/2024/01/1-2.png
800
1280
tridigitalSEO
/wp-content/uploads/2023/10/logo.svg
tridigitalSEO2024-01-25 17:51:002024-01-18 11:54:25Cybersecurity in the Age of AI: Transforming IT Solutions for Modern Businesses https://compsysplus.com/wp-content/uploads/2024/01/1-1.png
488
734
tridigitalSEO
/wp-content/uploads/2023/10/logo.svg
tridigitalSEO2024-01-23 15:45:002024-01-18 11:51:04Proven Tips for Effective IT Budgeting: Maximizing ROI for Your Business
https://compsysplus.com/wp-content/uploads/2024/01/1-1.png
488
734
tridigitalSEO
/wp-content/uploads/2023/10/logo.svg
tridigitalSEO2024-01-23 15:45:002024-01-18 11:51:04Proven Tips for Effective IT Budgeting: Maximizing ROI for Your Business https://compsysplus.com/wp-content/uploads/2024/01/Photo-realistic-image-of-a-Caucasian-male-cybersecurity-expert-in-his-30s-working-in-a-high-tech-digital-security-control-room.jpg
400
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-01-22 16:48:022024-01-15 16:51:33The Human Shield: Training Your Team Against Cyber Attacks with Computer Systems Plus
https://compsysplus.com/wp-content/uploads/2024/01/Photo-realistic-image-of-a-Caucasian-male-cybersecurity-expert-in-his-30s-working-in-a-high-tech-digital-security-control-room.jpg
400
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-01-22 16:48:022024-01-15 16:51:33The Human Shield: Training Your Team Against Cyber Attacks with Computer Systems Plus https://compsysplus.com/wp-content/uploads/2024/01/Photo-realistic-digital-illustration-depicting-a-modern-corporate-building-navigating-through-a-complex-labyrinthine-maze-representing-the-challenges-of-cybersecurity-regulations.jpg
400
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-01-19 16:41:132024-01-15 16:46:12Staying Compliant: How Computer Systems Plus Navigates Cybersecurity Regulations
https://compsysplus.com/wp-content/uploads/2024/01/Photo-realistic-digital-illustration-depicting-a-modern-corporate-building-navigating-through-a-complex-labyrinthine-maze-representing-the-challenges-of-cybersecurity-regulations.jpg
400
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-01-19 16:41:132024-01-15 16:46:12Staying Compliant: How Computer Systems Plus Navigates Cybersecurity Regulations https://compsysplus.com/wp-content/uploads/2024/01/1.png
492
744
tridigitalSEO
/wp-content/uploads/2023/10/logo.svg
tridigitalSEO2024-01-18 15:44:002024-01-18 11:47:37Driving Innovation: How IT Procurement Services Foster Technological Advancement
https://compsysplus.com/wp-content/uploads/2024/01/1.png
492
744
tridigitalSEO
/wp-content/uploads/2023/10/logo.svg
tridigitalSEO2024-01-18 15:44:002024-01-18 11:47:37Driving Innovation: How IT Procurement Services Foster Technological Advancement https://compsysplus.com/wp-content/uploads/2024/01/digital-shield.jpg
400
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-01-17 15:20:452024-01-11 15:24:50Understanding Intrusion Prevention Systems: Your Cybersecurity Guard
https://compsysplus.com/wp-content/uploads/2024/01/digital-shield.jpg
400
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-01-17 15:20:452024-01-11 15:24:50Understanding Intrusion Prevention Systems: Your Cybersecurity Guard https://compsysplus.com/wp-content/uploads/2024/01/Photo-realistic-image-depicting-a-digital-shield-symbolizing-Intrusion-Detection-and-Prevention-Systems-IDS-IPS-protecting-a-network.jpg
400
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-01-16 00:00:002024-01-16 15:35:44The Evolution of Cyber Threats and the Role of IDS/IPS
https://compsysplus.com/wp-content/uploads/2024/01/Photo-realistic-image-depicting-a-digital-shield-symbolizing-Intrusion-Detection-and-Prevention-Systems-IDS-IPS-protecting-a-network.jpg
400
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-01-16 00:00:002024-01-16 15:35:44The Evolution of Cyber Threats and the Role of IDS/IPS https://compsysplus.com/wp-content/uploads/2024/01/cybersec-digital-image.jpg
400
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-01-10 19:13:052024-01-11 15:20:25Next-Gen Intrusion Detection: Protecting Your Business in the Digital Age
https://compsysplus.com/wp-content/uploads/2024/01/cybersec-digital-image.jpg
400
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2024-01-10 19:13:052024-01-11 15:20:25Next-Gen Intrusion Detection: Protecting Your Business in the Digital Age https://compsysplus.com/wp-content/uploads/2023/10/Group-336-6.png
725
1366
essosdigital
/wp-content/uploads/2023/10/logo.svg
essosdigital2023-10-14 16:11:592023-10-22 19:37:2410 Reasons to Embrace a Third-Party Backup Solution for Microsoft Office 365 by Redstor
https://compsysplus.com/wp-content/uploads/2023/10/Group-336-6.png
725
1366
essosdigital
/wp-content/uploads/2023/10/logo.svg
essosdigital2023-10-14 16:11:592023-10-22 19:37:2410 Reasons to Embrace a Third-Party Backup Solution for Microsoft Office 365 by Redstor https://compsysplus.com/wp-content/uploads/2023/10/cover-1-e1674074577978-400x250-1.png
209
332
essosdigital
/wp-content/uploads/2023/10/logo.svg
essosdigital2023-10-14 16:11:182023-10-15 18:06:33SMALL Tech Businesses Can Make a BIG Impact on Earth Day
https://compsysplus.com/wp-content/uploads/2023/10/cover-1-e1674074577978-400x250-1.png
209
332
essosdigital
/wp-content/uploads/2023/10/logo.svg
essosdigital2023-10-14 16:11:182023-10-15 18:06:33SMALL Tech Businesses Can Make a BIG Impact on Earth Day https://compsysplus.com/wp-content/uploads/2023/10/AdobeStock_509757335-400x250-1.png
209
332
essosdigital
/wp-content/uploads/2023/10/logo.svg
essosdigital2023-10-14 16:10:462023-11-14 14:09:52Embracing Leadership: Empowering Business Success, No Matter Your Role
https://compsysplus.com/wp-content/uploads/2023/10/AdobeStock_509757335-400x250-1.png
209
332
essosdigital
/wp-content/uploads/2023/10/logo.svg
essosdigital2023-10-14 16:10:462023-11-14 14:09:52Embracing Leadership: Empowering Business Success, No Matter Your Role https://compsysplus.com/wp-content/uploads/2023/10/795a6d55-c9aa-4cb2-b2d8-0ada6f88d8fc_2023_MSP_501_Social_Graphics_1200x628-400x250-1.png
209
332
essosdigital
/wp-content/uploads/2023/10/logo.svg
essosdigital2023-10-14 16:10:082023-10-14 16:10:10Computer Systems Plus Ranked on Channel Futures 2023 MSP 501—Tech Industry’s Most Prestigious List of Managed Service Providers Worldwide
https://compsysplus.com/wp-content/uploads/2023/10/795a6d55-c9aa-4cb2-b2d8-0ada6f88d8fc_2023_MSP_501_Social_Graphics_1200x628-400x250-1.png
209
332
essosdigital
/wp-content/uploads/2023/10/logo.svg
essosdigital2023-10-14 16:10:082023-10-14 16:10:10Computer Systems Plus Ranked on Channel Futures 2023 MSP 501—Tech Industry’s Most Prestigious List of Managed Service Providers Worldwide https://compsysplus.com/wp-content/uploads/2023/10/The-Importance-of-Backup-and-Restore-400x250-1.png
209
332
essosdigital
/wp-content/uploads/2023/10/logo.svg
essosdigital2023-10-14 16:09:232023-10-14 16:09:23Redstor Presents: 9 Reasons You Need Third-Party Google Workspace Backup
https://compsysplus.com/wp-content/uploads/2023/10/The-Importance-of-Backup-and-Restore-400x250-1.png
209
332
essosdigital
/wp-content/uploads/2023/10/logo.svg
essosdigital2023-10-14 16:09:232023-10-14 16:09:23Redstor Presents: 9 Reasons You Need Third-Party Google Workspace Backup https://compsysplus.com/wp-content/uploads/2023/10/cover-1-e1674074577978-400x250-1.png
209
332
essosdigital
/wp-content/uploads/2023/10/logo.svg
essosdigital2023-10-14 16:08:262023-10-14 16:08:27Embracing the Joy of Networking: Building Connections
https://compsysplus.com/wp-content/uploads/2023/10/cover-1-e1674074577978-400x250-1.png
209
332
essosdigital
/wp-content/uploads/2023/10/logo.svg
essosdigital2023-10-14 16:08:262023-10-14 16:08:27Embracing the Joy of Networking: Building Connections https://compsysplus.com/wp-content/uploads/2020/02/it-support.jpg
632
1366
essosdigital
/wp-content/uploads/2023/10/logo.svg
essosdigital2023-10-09 21:31:582023-11-07 17:06:54Embracing the Joy of Networking: Building Connections
https://compsysplus.com/wp-content/uploads/2020/02/it-support.jpg
632
1366
essosdigital
/wp-content/uploads/2023/10/logo.svg
essosdigital2023-10-09 21:31:582023-11-07 17:06:54Embracing the Joy of Networking: Building Connections https://compsysplus.com/wp-content/uploads/2020/02/Group-1880.jpg
632
1366
essosdigital
/wp-content/uploads/2023/10/logo.svg
essosdigital2023-10-09 21:31:162023-10-09 21:31:17Brew Connect
https://compsysplus.com/wp-content/uploads/2020/02/Group-1880.jpg
632
1366
essosdigital
/wp-content/uploads/2023/10/logo.svg
essosdigital2023-10-09 21:31:162023-10-09 21:31:17Brew Connect https://compsysplus.com/wp-content/uploads/2023/10/cybersecurity-tips-980x528-1.jpg
528
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2023-03-28 06:51:002023-12-11 16:32:25Tips for Better Security
https://compsysplus.com/wp-content/uploads/2023/10/cybersecurity-tips-980x528-1.jpg
528
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2023-03-28 06:51:002023-12-11 16:32:25Tips for Better Security https://compsysplus.com/wp-content/uploads/2023/10/Advanced-Persistent-Threat-1080x630-1.webp
630
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2023-03-08 06:42:002023-10-26 06:44:42SOPHOS 2023 Threat Report
https://compsysplus.com/wp-content/uploads/2023/10/Advanced-Persistent-Threat-1080x630-1.webp
630
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2023-03-08 06:42:002023-10-26 06:44:42SOPHOS 2023 Threat Report https://compsysplus.com/wp-content/uploads/2023/10/Blog2-1080x631-1.jpg
631
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2023-02-22 06:37:002023-10-26 06:42:19Fool’s Gold: Dissecting a Fake Gold Market Pig-Butchering Scam
https://compsysplus.com/wp-content/uploads/2023/10/Blog2-1080x631-1.jpg
631
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2023-02-22 06:37:002023-10-26 06:42:19Fool’s Gold: Dissecting a Fake Gold Market Pig-Butchering Scam https://compsysplus.com/wp-content/uploads/2023/10/MDRPhoto-980x550-1.jpg
550
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2023-02-03 18:34:002023-10-26 06:35:55Is Sophos MDR really #1?
https://compsysplus.com/wp-content/uploads/2023/10/MDRPhoto-980x550-1.jpg
550
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2023-02-03 18:34:002023-10-26 06:35:55Is Sophos MDR really #1? https://compsysplus.com/wp-content/uploads/2023/10/blog-sophos-mdr-what-s-new-adam-gleeson.png
600
800
patm
/wp-content/uploads/2023/10/logo.svg
patm2023-01-11 18:33:002023-10-26 06:34:35Top 5 Reasons to Use SOPHOS MDR
https://compsysplus.com/wp-content/uploads/2023/10/blog-sophos-mdr-what-s-new-adam-gleeson.png
600
800
patm
/wp-content/uploads/2023/10/logo.svg
patm2023-01-11 18:33:002023-10-26 06:34:35Top 5 Reasons to Use SOPHOS MDR https://compsysplus.com/wp-content/uploads/2023/10/BlogCover-1080x627-1.jpg
627
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-12-28 16:08:002023-10-25 16:14:57So-Long, Farewell 2022
https://compsysplus.com/wp-content/uploads/2023/10/BlogCover-1080x627-1.jpg
627
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-12-28 16:08:002023-10-25 16:14:57So-Long, Farewell 2022 https://compsysplus.com/wp-content/uploads/2023/10/Laptop-Credit-Card-and-Christmas.jpeg
551
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-12-14 16:08:002023-10-25 16:10:04You’re a Mean one….Mr. Scammer
https://compsysplus.com/wp-content/uploads/2023/10/Laptop-Credit-Card-and-Christmas.jpeg
551
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-12-14 16:08:002023-10-25 16:10:04You’re a Mean one….Mr. Scammer https://compsysplus.com/wp-content/uploads/2023/10/NovemberBlog2-980x414-1.jpg
414
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-11-29 16:06:002023-10-25 16:08:10Redstor Introduces Backup for QuickBooks
https://compsysplus.com/wp-content/uploads/2023/10/NovemberBlog2-980x414-1.jpg
414
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-11-29 16:06:002023-10-25 16:08:10Redstor Introduces Backup for QuickBooks https://compsysplus.com/wp-content/uploads/2023/10/download-3.png
113
400
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-11-09 16:04:002023-10-25 16:06:14Rob on a Podcast?!
https://compsysplus.com/wp-content/uploads/2023/10/download-3.png
113
400
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-11-09 16:04:002023-10-25 16:06:14Rob on a Podcast?! https://compsysplus.com/wp-content/uploads/2023/10/2022-Legal-Trends-Report-980x490-1.png
490
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-10-18 13:00:002023-10-25 16:03:592022 Legal Trends Report
https://compsysplus.com/wp-content/uploads/2023/10/2022-Legal-Trends-Report-980x490-1.png
490
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-10-18 13:00:002023-10-25 16:03:592022 Legal Trends Report https://compsysplus.com/wp-content/uploads/2023/10/BlogCoverPhoto-980x465-1.jpg
465
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-09-28 15:39:002023-10-26 15:40:41When Partnerships Flourish
https://compsysplus.com/wp-content/uploads/2023/10/BlogCoverPhoto-980x465-1.jpg
465
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-09-28 15:39:002023-10-26 15:40:41When Partnerships Flourish https://compsysplus.com/wp-content/uploads/2023/10/1Featured.png
929
1314
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-09-12 16:00:002023-10-26 16:38:517 Reasons Why You Need A Separate Backup Strategy for Microsoft 365
https://compsysplus.com/wp-content/uploads/2023/10/1Featured.png
929
1314
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-09-12 16:00:002023-10-26 16:38:517 Reasons Why You Need A Separate Backup Strategy for Microsoft 365 https://compsysplus.com/wp-content/uploads/2023/10/CLio-Blog.jpg
500
750
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-08-31 18:21:002023-10-26 18:22:27How to Pick the Best Case Management Software for Your Law Firm
https://compsysplus.com/wp-content/uploads/2023/10/CLio-Blog.jpg
500
750
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-08-31 18:21:002023-10-26 18:22:27How to Pick the Best Case Management Software for Your Law Firm https://compsysplus.com/wp-content/uploads/2023/10/cyber-security-for-small-businesses-featured-800x400-1.png
400
800
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-08-17 15:21:002023-10-27 15:23:09Datto’s Nine Cybersecurity Tips Every Business Should Follow
https://compsysplus.com/wp-content/uploads/2023/10/cyber-security-for-small-businesses-featured-800x400-1.png
400
800
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-08-17 15:21:002023-10-27 15:23:09Datto’s Nine Cybersecurity Tips Every Business Should Follow https://compsysplus.com/wp-content/uploads/2023/10/SOPHOS-1080x628-1.webp
628
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-07-27 15:23:002023-10-27 15:24:48The State of Ransomware in 2022
https://compsysplus.com/wp-content/uploads/2023/10/SOPHOS-1080x628-1.webp
628
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-07-27 15:23:002023-10-27 15:24:48The State of Ransomware in 2022 https://compsysplus.com/wp-content/uploads/2023/10/data-backup-featured.jpg
450
1050
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-07-13 15:25:002023-10-27 15:26:12Protect the Data at All Cost!
https://compsysplus.com/wp-content/uploads/2023/10/data-backup-featured.jpg
450
1050
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-07-13 15:25:002023-10-27 15:26:12Protect the Data at All Cost! https://compsysplus.com/wp-content/uploads/2023/10/Computer-Cookies-848x480-1.jpg
480
848
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-06-16 18:24:002023-10-26 18:26:02And That’s the Way the Computer Cookie Crumbles
https://compsysplus.com/wp-content/uploads/2023/10/Computer-Cookies-848x480-1.jpg
480
848
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-06-16 18:24:002023-10-26 18:26:02And That’s the Way the Computer Cookie Crumbles https://compsysplus.com/wp-content/uploads/2023/10/Scale.jpg
367
612
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-05-27 18:27:002023-10-26 18:28:44Scale like You’ve Never Grown Before
https://compsysplus.com/wp-content/uploads/2023/10/Scale.jpg
367
612
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-05-27 18:27:002023-10-26 18:28:44Scale like You’ve Never Grown Before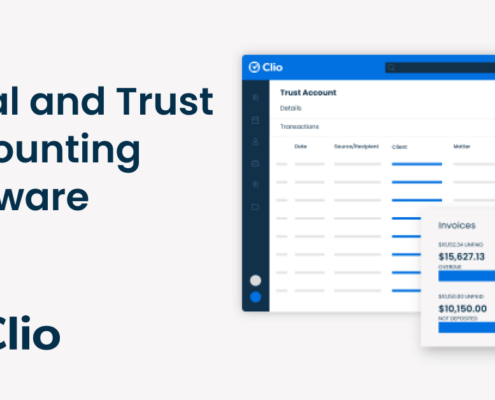 https://compsysplus.com/wp-content/uploads/2023/10/ClioPhoto-1080x628-1.png
628
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-05-09 18:26:002023-10-26 18:27:29Clio: Making Lawyer’s Jobs a Little Easier
https://compsysplus.com/wp-content/uploads/2023/10/ClioPhoto-1080x628-1.png
628
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-05-09 18:26:002023-10-26 18:27:29Clio: Making Lawyer’s Jobs a Little Easier https://compsysplus.com/wp-content/uploads/2023/10/ChangeGraphic.jpg
468
780
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-04-20 18:23:002023-10-26 18:24:44Nothing Changes if Nothing Changes
https://compsysplus.com/wp-content/uploads/2023/10/ChangeGraphic.jpg
468
780
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-04-20 18:23:002023-10-26 18:24:44Nothing Changes if Nothing Changes https://compsysplus.com/wp-content/uploads/2023/10/March22.jpg
640
960
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-03-22 15:31:002023-10-27 15:38:42Lawyers Heads Aren’t Up in the Cloud, but Their Law firm Should be
https://compsysplus.com/wp-content/uploads/2023/10/March22.jpg
640
960
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-03-22 15:31:002023-10-27 15:38:42Lawyers Heads Aren’t Up in the Cloud, but Their Law firm Should be https://compsysplus.com/wp-content/uploads/2023/10/March-9th.jpg
640
960
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-03-09 15:29:002023-10-27 15:30:27Sophos is just what the Doctor Ordered
https://compsysplus.com/wp-content/uploads/2023/10/March-9th.jpg
640
960
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-03-09 15:29:002023-10-27 15:30:27Sophos is just what the Doctor Ordered https://compsysplus.com/wp-content/uploads/2023/10/FebBlog2-980x653-1.jpg
653
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-02-24 15:27:002023-10-27 15:28:53Eject and Destroy!
https://compsysplus.com/wp-content/uploads/2023/10/FebBlog2-980x653-1.jpg
653
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-02-24 15:27:002023-10-27 15:28:53Eject and Destroy! https://compsysplus.com/wp-content/uploads/2023/10/Hacker-Thumb-a1.png
394
700
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-02-16 16:17:002023-10-27 16:22:50One Password to Rule them All? Better think Again.
https://compsysplus.com/wp-content/uploads/2023/10/Hacker-Thumb-a1.png
394
700
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-02-16 16:17:002023-10-27 16:22:50One Password to Rule them All? Better think Again. https://compsysplus.com/wp-content/uploads/2023/10/cybersecurity-masthead.jpg.pc-adaptive.full_.medium-1080x675-1.jpeg
675
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-01-21 16:38:002023-10-27 16:42:172022 Cybersecurity Tips for Everyday
https://compsysplus.com/wp-content/uploads/2023/10/cybersecurity-masthead.jpg.pc-adaptive.full_.medium-1080x675-1.jpeg
675
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-01-21 16:38:002023-10-27 16:42:172022 Cybersecurity Tips for Everyday https://compsysplus.com/wp-content/uploads/2023/10/https___specials-images.forbesimg.com_imageserve_60aebefe000f48e9d5646d20_0x0-1080x488-1.jpg
488
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-01-17 16:45:002023-10-27 16:46:27What Type of Player Do You Wanna Be in 2022?
https://compsysplus.com/wp-content/uploads/2023/10/https___specials-images.forbesimg.com_imageserve_60aebefe000f48e9d5646d20_0x0-1080x488-1.jpg
488
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2022-01-17 16:45:002023-10-27 16:46:27What Type of Player Do You Wanna Be in 2022? https://compsysplus.com/wp-content/uploads/2023/10/Cool-Future-Gadgets-800x445-1.jpg
445
800
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-12-20 17:03:002023-12-11 16:33:16Here are 6 Gadgets that you Might have Missed in 2021
https://compsysplus.com/wp-content/uploads/2023/10/Cool-Future-Gadgets-800x445-1.jpg
445
800
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-12-20 17:03:002023-12-11 16:33:16Here are 6 Gadgets that you Might have Missed in 2021 https://compsysplus.com/wp-content/uploads/2023/10/BlogCover-photo-1080x600-1.jpg
600
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-12-07 17:04:002023-10-27 17:06:0410 Tech Gifts that You’ll Want to Put on your Christmas List!
https://compsysplus.com/wp-content/uploads/2023/10/BlogCover-photo-1080x600-1.jpg
600
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-12-07 17:04:002023-10-27 17:06:0410 Tech Gifts that You’ll Want to Put on your Christmas List! https://compsysplus.com/wp-content/uploads/2023/10/Email-Header_2021-Legal-Trends-Report-Published-by-Clio.png
400
800
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-11-30 17:09:002023-10-27 17:10:53Legal Trends Report 2021
https://compsysplus.com/wp-content/uploads/2023/10/Email-Header_2021-Legal-Trends-Report-Published-by-Clio.png
400
800
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-11-30 17:09:002023-10-27 17:10:53Legal Trends Report 2021 https://compsysplus.com/wp-content/uploads/2023/10/working-from-home-vs-working-from-the-office-comparison-1-1200x675-1-1080x675-1.png
675
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-11-09 17:01:002023-10-27 17:02:30Is it Actually Better to Work from Home?
https://compsysplus.com/wp-content/uploads/2023/10/working-from-home-vs-working-from-the-office-comparison-1-1200x675-1-1080x675-1.png
675
1080
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-11-09 17:01:002023-10-27 17:02:30Is it Actually Better to Work from Home? https://compsysplus.com/wp-content/uploads/2023/11/Picture1-1.png
371
680
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-09-10 14:31:002023-11-02 14:34:53When It Comes to Screens…
https://compsysplus.com/wp-content/uploads/2023/11/Picture1-1.png
371
680
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-09-10 14:31:002023-11-02 14:34:53When It Comes to Screens… https://compsysplus.com/wp-content/uploads/2023/11/IMG_0163-980x895-1.jpg
895
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-09-02 14:50:002023-11-02 14:52:12Blood Drive Event 2021
https://compsysplus.com/wp-content/uploads/2023/11/IMG_0163-980x895-1.jpg
895
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-09-02 14:50:002023-11-02 14:52:12Blood Drive Event 2021 https://compsysplus.com/wp-content/uploads/2023/11/jacktrades.png
374
539
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-08-04 14:52:002023-11-02 14:53:35IT: Jack of all Trades Vs. Niche
https://compsysplus.com/wp-content/uploads/2023/11/jacktrades.png
374
539
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-08-04 14:52:002023-11-02 14:53:35IT: Jack of all Trades Vs. Niche https://compsysplus.com/wp-content/uploads/2023/11/cyber-security.png
554
843
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-07-23 14:24:002023-11-02 14:25:48Cybersecurity for Small Businesses
https://compsysplus.com/wp-content/uploads/2023/11/cyber-security.png
554
843
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-07-23 14:24:002023-11-02 14:25:48Cybersecurity for Small Businesses https://compsysplus.com/wp-content/uploads/2023/11/bec-blog.png
483
1070
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-07-08 14:26:002023-11-02 14:28:18The 10 Stages of a Business Email Compromise Attack
https://compsysplus.com/wp-content/uploads/2023/11/bec-blog.png
483
1070
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-07-08 14:26:002023-11-02 14:28:18The 10 Stages of a Business Email Compromise Attack https://compsysplus.com/wp-content/uploads/2023/11/Screen-Shot-2021-06-08-at-1.29.52-PM.png
557
969
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-06-08 14:28:002023-11-02 14:29:36IT Spring Cleaning
https://compsysplus.com/wp-content/uploads/2023/11/Screen-Shot-2021-06-08-at-1.29.52-PM.png
557
969
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-06-08 14:28:002023-11-02 14:29:36IT Spring Cleaning https://compsysplus.com/wp-content/uploads/2023/11/Blog-Graphic-980x551-1.png
551
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-01-26 14:16:002023-11-02 14:20:13Our Top 5 Memories of 2020
https://compsysplus.com/wp-content/uploads/2023/11/Blog-Graphic-980x551-1.png
551
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2021-01-26 14:16:002023-11-02 14:20:13Our Top 5 Memories of 2020 https://compsysplus.com/wp-content/uploads/2023/11/Knox-Chamber-Partnership-980x543-1.png
543
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-12-18 14:19:002023-11-02 14:22:05IT Support for Knoxville Chamber
https://compsysplus.com/wp-content/uploads/2023/11/Knox-Chamber-Partnership-980x543-1.png
543
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-12-18 14:19:002023-11-02 14:22:05IT Support for Knoxville Chamber https://compsysplus.com/wp-content/uploads/2023/11/Susannahs-house-3-980x735-1.jpg
735
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-12-15 14:22:002023-11-02 14:24:20Our Knoxville Non-Profit Christmas Donation!
https://compsysplus.com/wp-content/uploads/2023/11/Susannahs-house-3-980x735-1.jpg
735
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-12-15 14:22:002023-11-02 14:24:20Our Knoxville Non-Profit Christmas Donation!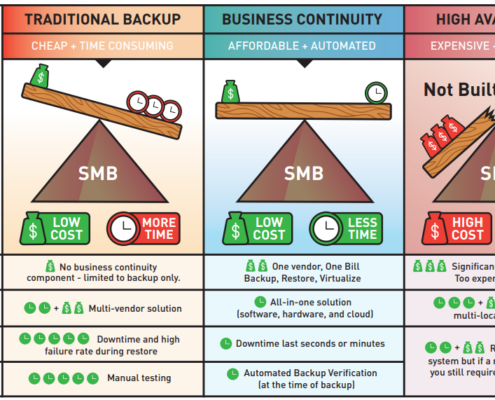 /wp-content/uploads/2023/10/logo.svg
0
0
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-08-19 17:39:002023-10-27 17:40:05Do I need an IT company?
/wp-content/uploads/2023/10/logo.svg
0
0
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-08-19 17:39:002023-10-27 17:40:05Do I need an IT company? https://compsysplus.com/wp-content/uploads/2023/11/South-high-assisted-living-project-review-980x551-1.png
551
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-07-31 14:54:002023-11-02 14:56:33Our recent review from Dover Signature
https://compsysplus.com/wp-content/uploads/2023/11/South-high-assisted-living-project-review-980x551-1.png
551
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-07-31 14:54:002023-11-02 14:56:33Our recent review from Dover Signature https://compsysplus.com/wp-content/uploads/2023/11/qtq80-cIs9xL-980x653-1.jpeg
653
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-07-23 14:57:002023-11-02 14:58:20What is good internet, anyways?
https://compsysplus.com/wp-content/uploads/2023/11/qtq80-cIs9xL-980x653-1.jpeg
653
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-07-23 14:57:002023-11-02 14:58:20What is good internet, anyways? https://compsysplus.com/wp-content/uploads/2023/11/cropped-JDH_1181-980x586-1.jpg
586
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-07-20 14:58:002023-11-02 14:59:51Why do you need an IT Provider?
https://compsysplus.com/wp-content/uploads/2023/11/cropped-JDH_1181-980x586-1.jpg
586
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-07-20 14:58:002023-11-02 14:59:51Why do you need an IT Provider? https://compsysplus.com/wp-content/uploads/2023/11/cybersecurity-scaled-1-980x653-1.jpg
653
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-05-12 15:01:002023-11-02 15:02:22Barbara Corcoran scammed for almost $400k
https://compsysplus.com/wp-content/uploads/2023/11/cybersecurity-scaled-1-980x653-1.jpg
653
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-05-12 15:01:002023-11-02 15:02:22Barbara Corcoran scammed for almost $400k https://compsysplus.com/wp-content/uploads/2023/11/zoom-scaled-1-980x735-1.jpg
735
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-05-08 15:05:002023-11-02 15:07:06New Questions for a New World – From the desk of Rob Glass, our CEO
https://compsysplus.com/wp-content/uploads/2023/11/zoom-scaled-1-980x735-1.jpg
735
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-05-08 15:05:002023-11-02 15:07:06New Questions for a New World – From the desk of Rob Glass, our CEO https://compsysplus.com/wp-content/uploads/2023/11/covid-blog-voer-980x231-1.png
231
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-05-08 15:04:002023-12-11 16:34:35When COVID happened – Rob Glass, CEO
https://compsysplus.com/wp-content/uploads/2023/11/covid-blog-voer-980x231-1.png
231
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-05-08 15:04:002023-12-11 16:34:35When COVID happened – Rob Glass, CEO https://compsysplus.com/wp-content/uploads/2023/11/CLean-up-your-IT-1-980x653-1.jpg
653
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-02-07 15:08:002023-11-02 15:10:13Clean up your IT
https://compsysplus.com/wp-content/uploads/2023/11/CLean-up-your-IT-1-980x653-1.jpg
653
980
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-02-07 15:08:002023-11-02 15:10:13Clean up your IT https://compsysplus.com/wp-content/uploads/2023/11/Untitled-design-6.png
313
643
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-02-07 15:07:002023-11-02 15:08:382-Factor Authentication
https://compsysplus.com/wp-content/uploads/2023/11/Untitled-design-6.png
313
643
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-02-07 15:07:002023-11-02 15:08:382-Factor Authentication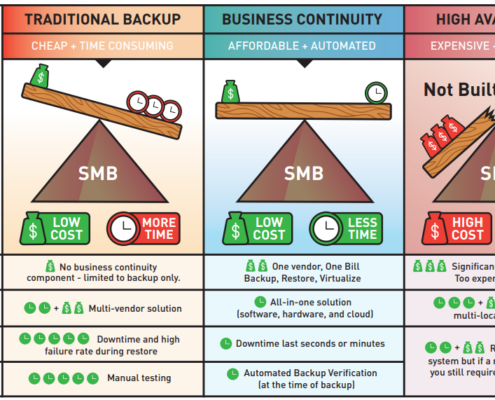 https://compsysplus.com/wp-content/uploads/2023/11/datto-image.png
571
1024
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-01-22 15:10:002023-11-02 15:11:43What is Business Continuity?
https://compsysplus.com/wp-content/uploads/2023/11/datto-image.png
571
1024
patm
/wp-content/uploads/2023/10/logo.svg
patm2020-01-22 15:10:002023-11-02 15:11:43What is Business Continuity?Contact Us
100 Dalton Place Way
Suite 101 | Knoxville, TN 37912
Phone:
865-573-5303Stay updated with us!
Sign up for the latest in IT solutions and special offers.